
Digital detox or Doctor, I’m attached to my smartphone — is it normal?
How did you like it the last time you saw your friends? Did you have a nice chat with them? Or were you all only taking pictures of your meals to post them on Instagram and talking to each other on Facebook?
 #tips
#tips
 BYOD
BYOD
 books
books

 cameras
cameras
 apple
apple

 #advice
#advice





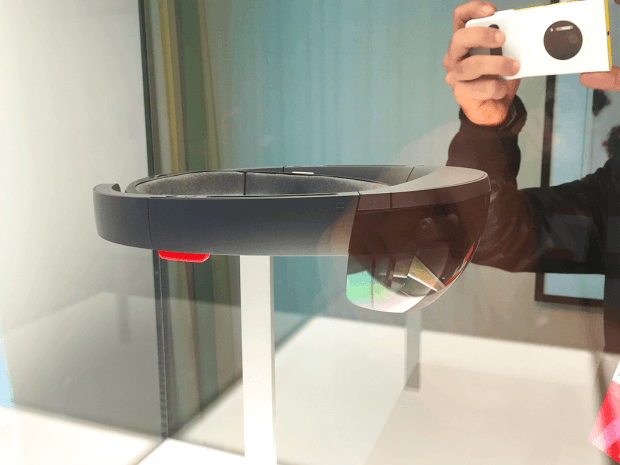
 3D
3D




