
How easy is it for hackers to steal your face?
Fingerprints and iris scans are insecure and can be stolen to compromise your identity.
4143 articles

Fingerprints and iris scans are insecure and can be stolen to compromise your identity.

The latest research by Kaspersky Lab and B2B International shows that 33% of financial services organizations don’t offer customers a secure channel for all of their online payments, despite the fact that most have noticed a significant rise in customers making online financial transactions.

Do you think that you have nothing to hack whatsoever? Bad news, guys: everyone has something hackable!

Since mid-October, several major software vendors have released a number of security announcements and updates, most of them serious or outward critical.
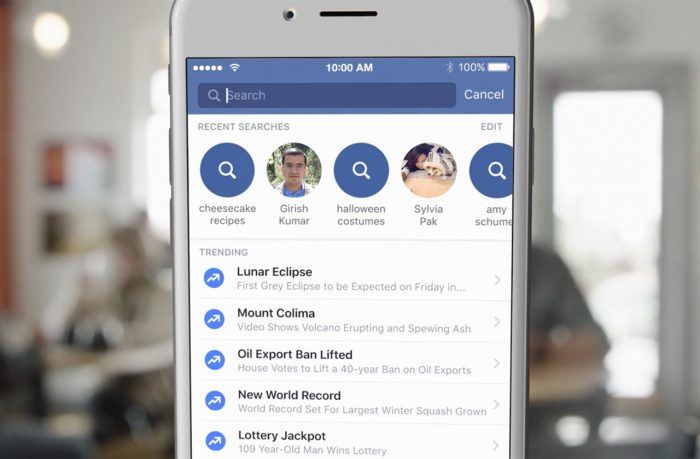
Stop what you are doing and check your privacy settings on Facebook.

We interview Russia’s youngest grand master. He reveals the story of falling in love with chess, the strategy and the tactics of the game, and plans for the future.

Kaspersky Lab has patented a new technology designed to prioritize data-scanning tasks on virtual machines. The technology significantly speeds up processing of high-priority scan requests in real time, while maintaining virtual machine performance.

The world is a reality TV show and sometimes we cannot resist the opportunity to snap up our piece of fame. We are posting funny pics of ourselves to amuse

Apple users say their Macs are a more secure working tool than Windows-based PCs. Unfortunately, it’s not exactly true.

With all of the hacks in the news, you may feel scared to shop online. Kaspersky Lab can ease your fears with the Safe Money feature of Kaspersky Internet Security 2016.

A new survey shows that businesses worldwide increasingly lose their faith in third-party suppliers. The reason? The increasing number of IT security incidents that they cause.

In Back to the Future 2, Marty McFly and co. come to 2015. Let’s see, which forecasts of this legendary saga are true and which are false.

Google’s Android OS is a vulnerable system. Developers make it worse by not providing critical patches in time.

A botnet behind Dridex, a sophisticated banking malware stealing credentials of online bank accounts worldwide, are down.
Konstantin Goncharov explains the bottom line of tech giants’ epic fails in the new edition of cybersecurity news digest.

Kaspersky Lab CEO answers questions from our social media community

New research by Kaspersky Lab shows that in the last 12 months every fourth Internet user had at least one of their online accounts hacked.
How to use a special app to protect your kids from unwanted calls and mobile fraud and be sure that your child is not playing online instead of studying.

What if you could be sure that your kids use Internet safely while their mobile phones are protected from fraud, unwanted calls and SMS? All you need for that is Kaspersky Safe Kids!

Why working in Kaspersky Lab has always been more than just business.

Threatpost had a story last week describing a disruption of a large ransomware campaign connected to the Angler exploit kit. Experts from Cisco’s Talos security group “effectively nillified 50 percent of the exploit kit’s activity”.