
If only the Internet starred in sci-fi movies
Blockbusters, like Star Wars or Independence Day, tell us breathtaking stories in which space blasters, force fields and traveling faster than the speed of light are all commonplace. But there
3952 articles

Blockbusters, like Star Wars or Independence Day, tell us breathtaking stories in which space blasters, force fields and traveling faster than the speed of light are all commonplace. But there

Kaspersky Labs security products have taken home multiple awards from independent testing groups in recent weeks, and that trend continued with the announcement that its Android smartphone solution, Kaspersky Mobile

Afraid you missed out on some of our blog posts this June? Not to worry, we’ve compiled highlights from our most popular Kaspersky Daily articles for you! Take a look:
We’ve already told you how to prevent your kids from accessing unwanted data online with tutorials on how to block access to specific websites and how to control file downloading. But aside from

Imagine the following situation: there is huge disbursement of emails with innocent looking MS Word document attachments sent to the mailboxes of a company’s employees. Some of these employees have

According to Kaspersky Labs research, 34 percent of worldwide Internet users were attacked by malicious programs in 2012. As always, the most popular entries for attackers were widely used programs
Extortion, blackmail and ransom requests have always been cornerstones of criminal activity. In today’s global internet economy, criminals are adapting their techniques by attempting to extort money from people using

We’re continuing to watch how law enforcement agencies around the world are progressing in the fight against cybercrime. They’ve been able to keep jailing hackers, both for minor cybercrimes like

Chances are you have more digital assets than you think. Everything from email and social media accounts, to online financial accounts, domain names, digital media collections (music and movies), and

14 finalists, 10 countries, 5 regional heats: and one London Final. We are still flying high from all the excitement generated by the ideas, innovation and inspiration that underpinned the

Have you ever wondered what a hacked computer, email address, or other online account is even worth? Sure, it seems pretty obvious that there’d be some serious value in a

Imagine the following situation: you have configured Kaspersky PURE to get the maximum protection for your computer, customized the settings of each component, specified which data should be backed up

There are many requests sent into Kaspersky Lab Technical Support concerning license issues for Kaspersky Anti-Virus, Kaspersky Internet Security and other products. Let’s discuss the top 10 most frequently asked

There is an entire market of plugins out there designed to keep you safe while surfing the web on your browser of choice. Each one has lots of options; for
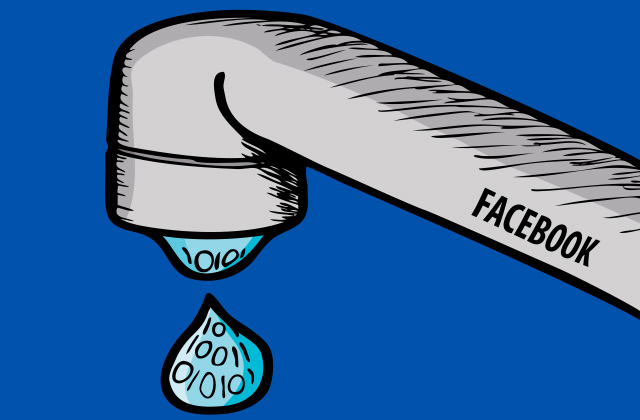
The recent incident of personal data being leaked from Facebook’s servers is just one more demonstration that even the best cloud services are not flawless. Therefore, every user should have

A newly discovered vulnerability in a popular browser exposes how photos can be taken of unsuspecting users. Further proof of hackers’ inventiveness appeared last week in the form of a

In late 2011, it emerged that Chinese hackers had thoroughly compromised the United States Chamber of Commerce, perforating the lobbying-group’s networks with a devastating chain of backdoors. Chamber officials admitted

What should have been a fairly straightforward climb for Olga Rumyantseva turned out to be a little harder than expected. Despite the difficulties the highest volcano in Asia gave Olga,
It’s harder and harder to keep your personal information private when browsing the web, but fortunately there is an entire market of add-on utilities, known as plugins, designed to keep

Apart from limiting access to specific websites, thus protecting your child from getting unrestricted information from the web, Parental Control in Kaspersky PURE 3.0 can save your child from downloading

Monaco is a symbol of the high life. Spend some time in Monte-Carlo and you will see why it is a respected home for the richest people in the world