
Inside Out vs. Outside In
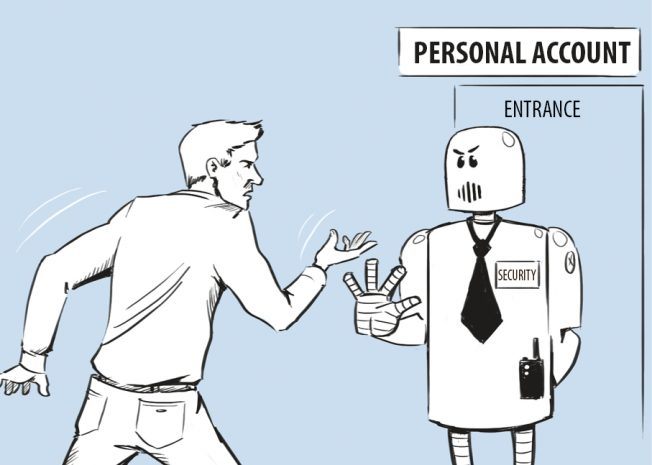
When we think of information security, we tend to think of external hackers and cyber-criminals fighting their way inside an organisation’s network to steal its information. Clearswift commissioned some research
3952 articles

When we think of information security, we tend to think of external hackers and cyber-criminals fighting their way inside an organisation’s network to steal its information. Clearswift commissioned some research

Everyone who has ever seen the sunset at the foot of Damavand says they’ve never witnessed anything more beautiful. The beauty and greatness of Damavand are both expressed in numerous
We aren’t robots and we are here to help. We respect you and your tech support questions.

There’s been something of an uneasy consensus among experts that Apple’s iOS platform is the most secure option among mobile operating systems almost exclusively because of the closed-off nature of

Targeted attacks gain popularity as a means of cyber-espionage. They get more complex, use sophisticated algorithms and act more stealthily than ever. Even U.S. President Barack Obama voiced his concerns

Father’s Day is fast approaching, which means finding the perfect gift for dad should be at the top of your to do list. And if you’ve had your eye on

Security professionals and enthusiasts are aware of rootkits, but general audiences typically don’t know about this kind of malware, which is specifically designed to hide itself and its activity in

It’s one thing for an Internet protection suite to claim it has first-class levels of protection, but it is quite another thing when a security platform is found by independent

When surfing the Internet we click hundreds of links in search results and on web resources. How can you identify whether links are malicious or not? How can you be

Congratulations to our second stage winner in Kaspersky Lab’s 7 Volcanoes contest – Richa from India! Though Richa has traveled outside of India before, she has always dreamed of the

APT stands for advanced persistent threat. It became famous following a New York Times exposé detailing a month’s long attack campaign in which a Chinese military unit now known as

Kaspersky Lab held its first annual Government Cybersecurity Forum in Washington, D.C. earlier this week. The overarching conversation related to cybersecurity trends and what America (and other nations) should do

It can be very tempting to instantly share the most exciting moments of your vacation with relatives and maybe make your friends a little bit jealous. That’s why we usually

Kaspersky Lab’s security experts have published the first part of a new study of large scale cyber espionage campaign, called NetTraveler, which aimed at 350 large commercial and government organizations

The Internet has revolutionized the way we book our holidays. Unfortunately it is also enabling fraudsters to prey upon people’s desires to have a perfect vacation, so stay vigilant and

Almost all computer security instructions, whether it is a help page on Facebook, corporate regulations or part of the “… for dummies” series, urge us to use strong passwords at

If Achilles’s heel was his vulnerability in the Iliad, then Paris’s poison tipped arrow was the exploit. Quite literally, an exploit is the device or – more often than not

Another day, another online service adds two-factor authentication to its list of features. This time it was Evernote, the cloud-based note-taking service that hackers managed to compromise and use as

An agenda-packed conference with bright minds and eager speakers paired with an equally excited audience set the stage for Kaspersky Lab’s first annual Cybersecurity Government Forum in Washington, D.C. on

Today it’s difficult to imagine our lives without the Internet. The Internet gives access to modern music, new movies and videos, educational dictionaries, encyclopedias and articles. Children around the world