
Cybercrime, Inc.: how profitable is the business?
Cybercrime is a rather lucrative business. Cybercriminals are earning a lot, or at least their effort-to-profit rate is good enough for them to keep going. But how good is it?
833 articles

Cybercrime is a rather lucrative business. Cybercriminals are earning a lot, or at least their effort-to-profit rate is good enough for them to keep going. But how good is it?

Online games these days are products of years of development with budgets approaching those in Hollywood, and with similar marketing support. And if we speak of massively multiuser online games
Recent news concerning “hacked webcams” or “breached baby monitors” appears to be all over the place. Let’s take a closer look at the situation.

Medieval doors were extremely sturdy due to their two-layer construction and different wood grain directions across those layers. Multilayered defensive structures is a must in cybersecurity as well.

By default, your iPhone’s OS is set to give you the best performance instead of the best battery life. But you can change that!

Securelist has published extensive research on BlackEnergy. Initially a DDoS crimeware, it turned into a huge collection of various tools currently used in various APT-type activities, including some “significant geopolitical operations”.
Kaspersky Lab has just announced the discovery of an alarming APT campaign codenamed “Darkhotel,” targeted mainly at business executives staying at certain hotels in Asia. Luxury hotels offer not just places to stay, but also comfort and privacy. However, their cybersecurity occasionally fails.
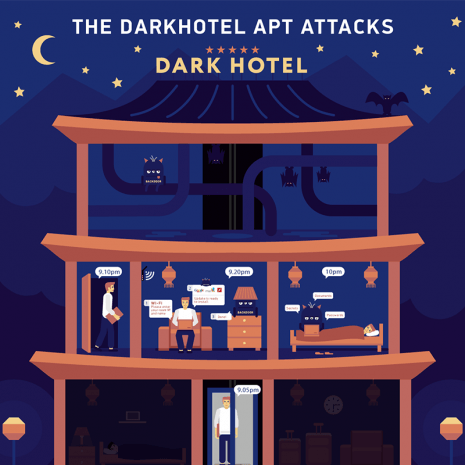
Kaspersky Lab revealed a cyberspy campaign, Darkhotel, which had been active for seven years in a number of luxury Asian hotels.

Let’s take a look at the security features in the new version of Mac OS X – Yosemite. Apple certainly makes a decent effort.

Internal and external threats may be quite different in nature, but they demand equal attention from the IT staff in order for the protection to be complete.

We’re taking a look at the security features in the new version of Mac OS X – Yosemite. Apple makes a decent effort.

Hotels offer not just free WiFi but occasionally even free use of devices such as iPads these days. While it is really nice, a misconfigured device like this may store just a bit too much personal data, easily retrievable by the next visitor…

Linux bugs may affect or directly threaten entire virtualization infrastructures: Whatever OS is used on VMs, an attack on a hypervisor is possible from both the outside and inside, and exploitation of the dreaded Shellshock vulnerability on Linux-based hypervisors is a possibility, too.
Can a business be “partially” prepared to ward off cyberthreats? That’s up for debate, but it seems there is little difference between “partial protection” and no protection at all.
Vulnerabilities vary. Some are considered critical, some – less problematic; their severity is determined by a few well-known factors such as ease of exploitability and popularity of software. But, no matter their differences they all require serious attention at a constant level, so that when the next Shellshock-like incident occurs, it won’t take cybersecurity world by surprise.

APT is a term often mentioned in cybersecurity bulletins. Here’s what you need to know to understand it.

Your primary email account is often the master key that can provide backup access to all other accounts, which is why you must be particularly careful with it.

Elena Kharchenko, Head of Consumer Product Management, answers the important security questions that you submitted.

You can manually set up Safe Money with ease even if your bank or payment system is not included in our database.

Like it or not, your children are going to be on the web. Kaspersky’s award-winning parental controls let you monitor their activity and block them from any sites that you choose.