Protection from banking “phishers”
You do not often read “repentance” articles in the media when authors describe as they did something evidently stupid and paid for it. Last year one such piece was published
833 articles
You do not often read “repentance” articles in the media when authors describe as they did something evidently stupid and paid for it. Last year one such piece was published

According to Kaspersky Labs research, 34 percent of worldwide Internet users were attacked by malicious programs in 2012. As always, the most popular entries for attackers were widely used programs
Extortion, blackmail and ransom requests have always been cornerstones of criminal activity. In today’s global internet economy, criminals are adapting their techniques by attempting to extort money from people using

Have you ever wondered what a hacked computer, email address, or other online account is even worth? Sure, it seems pretty obvious that there’d be some serious value in a
The recent incident of personal data being leaked from Facebook’s servers is just one more demonstration that even the best cloud services are not flawless. Therefore, every user should have

Monaco is a symbol of the high life. Spend some time in Monte-Carlo and you will see why it is a respected home for the richest people in the world

When surfing the Internet we click hundreds of links in search results and on web resources. How can you identify whether links are malicious or not? How can you be

APT stands for advanced persistent threat. It became famous following a New York Times exposé detailing a month’s long attack campaign in which a Chinese military unit now known as

Kaspersky Lab’s security experts have published the first part of a new study of large scale cyber espionage campaign, called NetTraveler, which aimed at 350 large commercial and government organizations

The Internet has revolutionized the way we book our holidays. Unfortunately it is also enabling fraudsters to prey upon people’s desires to have a perfect vacation, so stay vigilant and

If Achilles’s heel was his vulnerability in the Iliad, then Paris’s poison tipped arrow was the exploit. Quite literally, an exploit is the device or – more often than not

Twitter has recently caught up with competitors like Facebook and Google by improving user protection with two-factor authentication. This will help us all forget about those much talked about account

When you purchase products via the Internet, manage bank accounts and eWallets, cyber criminals may steal your personal data. One of the best methods to secure your accounts is to

Microsoft (and Adobe for that matter) released a slew of security updates in the May 2013 edition of their monthly patch Tuesday release. As always, if your machine isn’t set

Over the last 9 years Facebook has grown from a small social networking site originally intended for college students into a worldwide platform that is now used not only by

Given the deftness of malicious hackers, the bar-lowering impact of easily accessible markets for automated cybercriminal kits, and the increasing number of online services and people connected to the Internet,
New technological business trends are almost always about investment. First you pay money and after that, if you get lucky, you make your employees happier, achieve tighter security of business

LivingSocial informed its millions of customers over the weekend that malicious hackers had compromised the popular coupon site’s computer systems, exposing the names, email addresses, dates of birth, and encrypted

As Infosecurity Europe 2013 draws to a close, we take a look at the key takeaways, trending topics and buzzwords from this year’s event. To coincide with Infosec, Verizon released

Organized cybercriminals have become adept at accessing consumers’ online bank accounts, exploiting either vulnerabilities in the Web-based application you access from your home computer or mobile device, or weak and
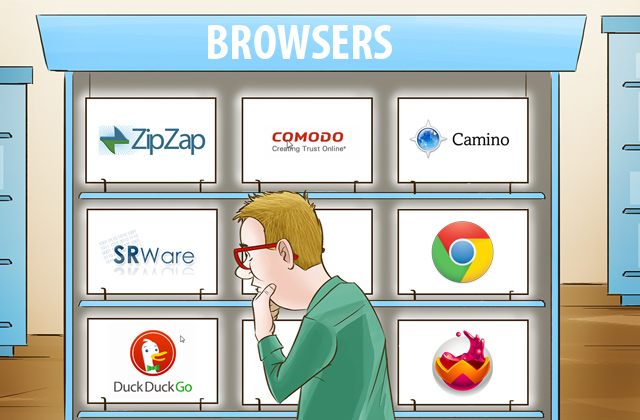
At this point, Internet Explorer, Google Chrome, Safari, and Mozilla Firefox are all modern, functional, and perfectly serviceable Web browsers. They each offer a robust set of interesting features, extensions,