
Lessons from the Bybit hack: how to store crypto safely
Takeaways for regular crypto holders from the biggest crypto heist in history.
43 articles

Takeaways for regular crypto holders from the biggest crypto heist in history.

Everything you wanted to know about meme cryptocurrencies — such as TRUMP and DOGE — and ways to win or lose big.
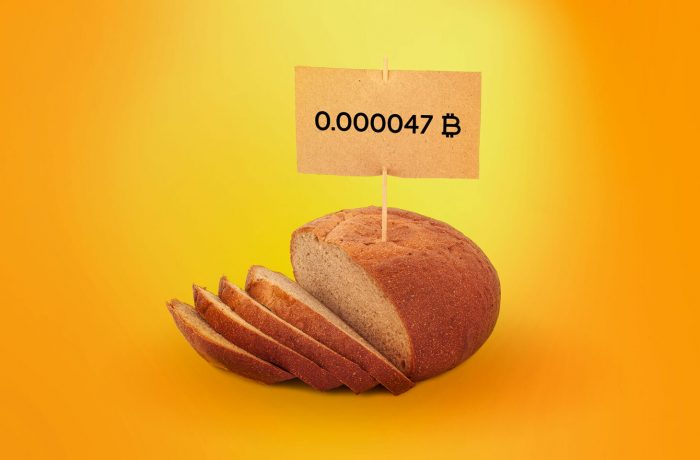
Scammers have invented a new trick — they post cryptowallet seed phrases in YouTube comments using newly created accounts. Here’s how it works

“Gentle grafters” are attacking dishonest crypto users by imitating wallet leaks and manipulating their victims for months.

Today we’re talking about crypto drainers — one of the most serious threats to crypto owners — and offer tips on fending it off.

Bitcoin wallets created on online platforms between 2011 and 2015 may be insecure due to a vulnerability in the library for key generation.

Crypto Olympics, or the full gamut of blockchain attacks: the biggest, most sophisticated, most audacious cryptocurrency heists of all time.

We explain how the advanced malware DoubleFinger downloads GreetingGhoul, a stealer that preys on cryptocurrency wallets.

Crypto mixers, nested exchanges, cash-out and other crypto-laundering methods used by ransomware operators.
Full review of a fake cryptowallet incident. It looks and feels like a Trezor wallet, but puts all your crypto-investments into the hands of criminals.

Hardware crypto wallets are effective at protecting your cryptocurrency, but they can still be stolen from. Let’s address the risks their owners need to be protected from.

How to reliably protect your cryptocurrency given the numerous fraud schemes and lack of protection through government regulation.

In the final part of the series, we take a look at cryptocurrency politics, the future, and the metaverse.

Hundreds of millions of dollars stolen: the five biggest heists in cryptocurrency history.

On this edition of the Kaspersky podcast, we discuss NFTs with Ivan Kwiatkowski in terms of what they are and if they are a scam.

In this second part of the series, we’re going to dive deep into Ethereum and its novelties: smart-contracts, DAOs and NFTs.
Everything you’ve always wanted to know about crypto on the whole, and NFTs in particular, and also why I’m not a fan of such tech, to say the least.

We explain how scammers steal cryptowallets through phishing.

Hans Christian Andersen’s report on the Kai infection incident, and the investigation by infosec expert Gerda.

While auditing Web applications, our experts found a vulnerability to enumeration attacks. Here is a description of the problem and how to combat it.

Dave and Jeff discuss MI5 pushing for weak encryption, the EU commission telling employees to use Signal, smart pet feeders going offline, and more.