
One dollar lesson: defend your buck from online fraud
One dollar lesson is a new interactive project by Kaspersky Lab that aims to help you stay protected from online money frauds. Learn three simple lessons right now!
669 articles

One dollar lesson is a new interactive project by Kaspersky Lab that aims to help you stay protected from online money frauds. Learn three simple lessons right now!

Brian Donohue and Chris Brook of Threatpost discuss Kaspersky Lab’s Security Analyst Summit, which took place last week in Cancun, Mexico

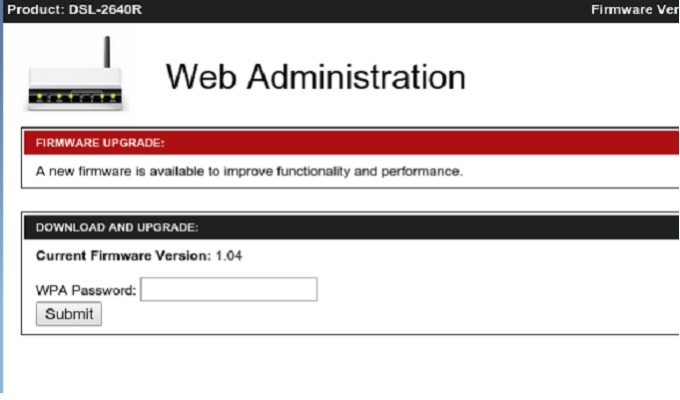
It turned out that Lenovo’s laptops had been shipped with an adware called Superfish. It possibly allows eavesdropping on encrypted connections
Today we discuss the most important news on information security from January.

Let’s talk about the dangers of cross-border payments with plastic cards and security flaws in payment systems architecture.

The Carbanak APT group managed to steal a total of $1 bln from dozens of banks worldwide

In this talk security podcast, Chris Brook and Brian Donohue discuss the upcoming Security Analyst Summit, Flash zero days, the Ghost vulnerability and the Anthem breach

WhatsApp has finally released a Web version of its popular mobile messaging service. We take a look at it from the security perspective.
The Internet continues to find its way into the private lives of its users. Here, we brief you on the most common methods of online tracking.

Whether you’re buying or selling a secondhand Apple device, you can be fooled by criminals. We have gathered tips on how to minimize your chances of being taken by such frauds.

As is, a QR code can quickly take you to a site or another resource but not necessarily to the one you really want to visit. Thus Kaspersky Lab offers a free and safe QR scanner!

Have you ever wondered how a typical office would look in a decade or so? Allow us to take you on a small tour of the most interesting office concepts.

The top privacy data leaks in 2014 include: data breaches at Target and Home Depot, hacks of JP Morgan and Barclays banks, and leaks at Orange and Dropbox.

Security reporters Brian Donohue and Chris Brook discuss security and privacy headlines from the first few weeks of the new year.

“British Prime Minister David Cameron to Ban Encrypted Messengers” — Headlines like this are appearing here and there. But what happened exactly?

CES 2015 was a superb event in terms of the amount of new technology per square foot. But, from an information security standpoint, it did not appear all that positive.
We collected the 10 best tweets related to an IT security event in 2014.

Gaming is enormously popular. Thus, it’s an easy target for cybercriminals looking for a never-ending source of money.
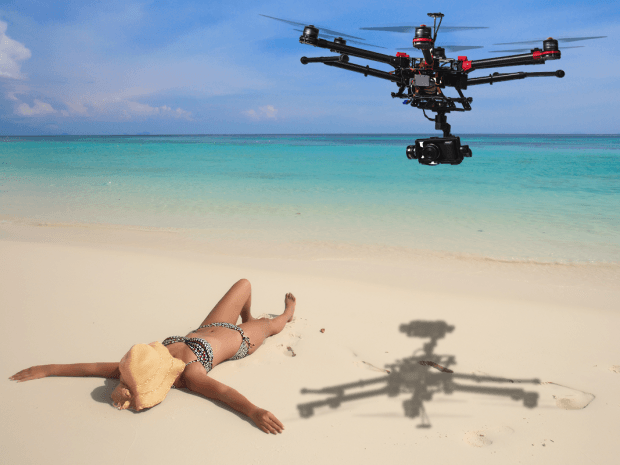
On the one hand, drones are bound to violate privacy, whether on purpose or not. On the other, we’ve yet to discover and unleash their full potential.

Anyone who goes online could be hacked. During Christmas time, this possibility doubles as we make a number of purchases and get so excited that we forget about security.

A new variant of the Zeus banking trojan has emerged, targeting consumer accounts at 150 banks in 15 countries.