
Transatlantic Cable podcast: Raising a digital native
In this special edition of the Kaspersky Lab podcast, we discuss how parents should look at raising digital natives and the precautions they need to take.
669 articles

In this special edition of the Kaspersky Lab podcast, we discuss how parents should look at raising digital natives and the precautions they need to take.

Freelancers are beloved targets for cybercriminals, who use phishing and malware to steal credentials and money. Here’s how to avoid their traps and stay safe.

Let’s talk about mobile malware that can empty your bank account or spy on you.
We explain what a guest Wi-Fi network is, how to set one up, and what video game consoles and other IoT devices have to do with it.

Fortnite for Android is not available on Google Play. We explain how to download and install it properly, and what else to do to stay safe.

In this part, we consider mobile malware capable of causing real damage to smartphone and tablet users.

More than 400 manufacturing companies became phishing targets.

58% of small and medium-size companies use various public-cloud-based business applications to work with customer data.

What’s new in the Kaspersky 2019 product lineup? Speed, security, and design improvements.

Kaspersky hogs the CPU, collaborates with the KGB, and writes viruses? We bust these myths and explain their origins.

No PIN on your phone? Pickpockets will thank you for that.

In part one of our mobile malware series, we cover infectious Android malware — adware, subscribers, and flooders — and how mobile viruses can damage your smartphone or tablet…
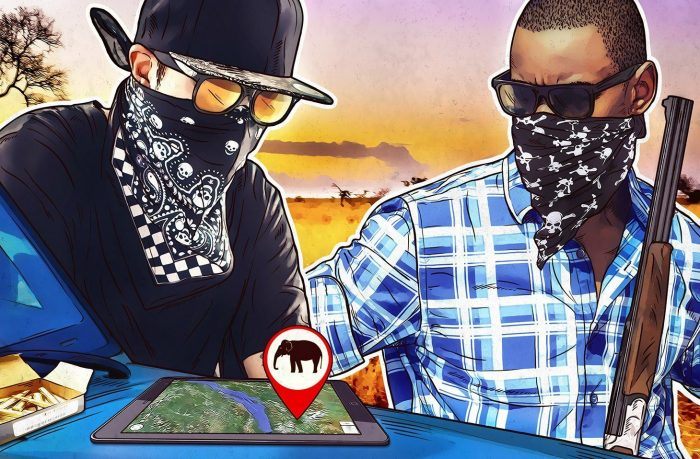
How tools designed to study and protect rare species can turn from gamekeeper to poacher.

Did you see that new fully loaded Android smartphone, the one that looks too good for the price? Well, it may include some unwanted extras.

Advertising in voice assistants is coming soon. We examine how it will use personal data and what you can do about it.

Here’s how scammers try to phish for verification codes — and what may happen if you send them one.

Do you follow the news? The news may also be following you. ZooPark spyware targets those partial to politics.

Stress relating to technology and cybersecurity is an escalating issue we can’t escape.